A long overdue congratulations to Dr. Peter Tueller for successfully defending his Ph.D.
Peter joined our group in Fall 2016 despite me doing one of the worst recruiting jobs ever. He was doing outstanding undergraduate research to build a fleet of underwater vehicles. Around the same time, we were developing localization algorithms for swarms of underwater vehicles. It seemed like a perfect fit! I saw his UCSD graduate application many times — several colleagues forwarded it to me saying that I should make sure not to miss it. At the time I was on a sabbatical and not looking to take on more students. After the third or fourth time of someone telling me I should check out his application, I finally got around to it. I made him a very late offer, which was right before visit day. I asked if he could come and stick around another day so that I could meet him as I was traveling during the official visit days (again, I wasn’t planning on taking students that year).
Our first meeting still sticks in my mind. We met up at a taco restaurant in La Jolla Shores. I figured I didn’t have much of a shot at convincing him to come to UCSD. I was apologizing for making a late offer, not being a visit day, etc., but also trying my best to convince him that I was still really interested in working with him. I was doing a terrible job of recruiting him. But he rather nonchalantly stated that he was planning to come to UCSD. Lucky me!
Peter had a Ph.D. career that I will forever be jealous of. He spent a couple of months at the University of Haifa in Israel working with Roee Diamant on an underwater sonar project. He made expeditions to Guatemala to perform 3D scanning at the archaeological sites of El Zotz and Tikal. He worked most summers at NIWC Pacific developing different underwater technologies. He was the leader and driving force behind getting the FishSense project up and running. He got a SMART scholarship that allowed him to pursue Ph.D. research largely of his choosing related to 3D vision systems. This allowed him to move directly into a job at NIWC after graduation, which was what he wanted to do all along.
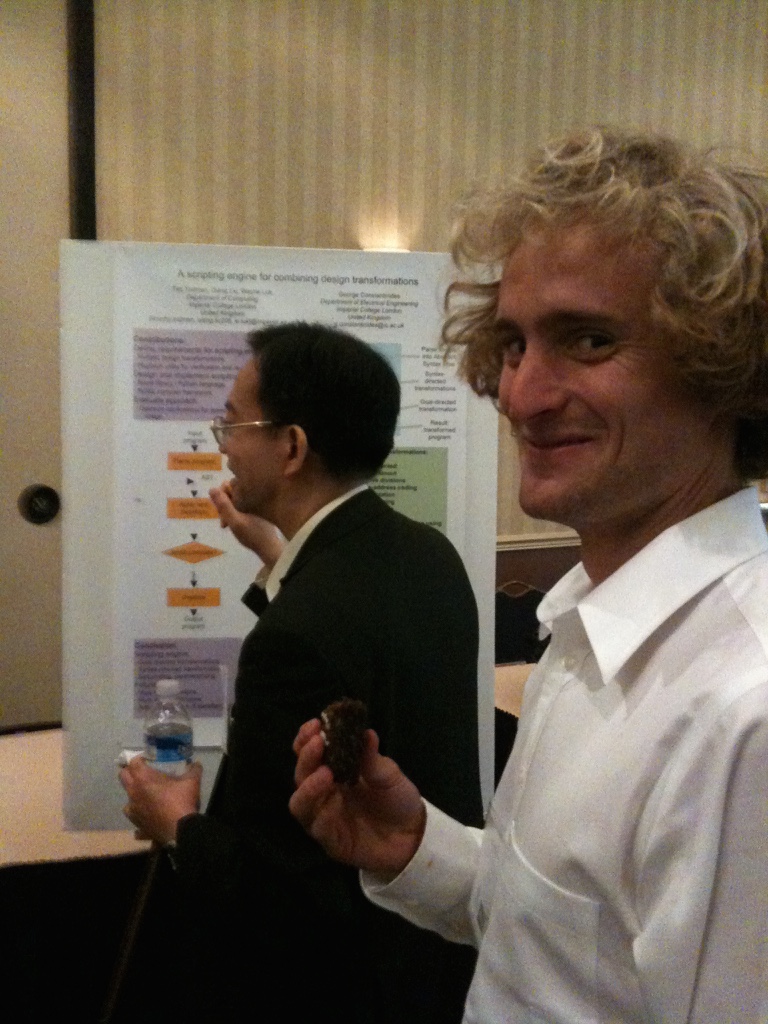
And all of this was done as a second career to being a rock star.
Despite being a rock star, Peter was a cool and calming influence on our group. I always looked forward to our weekly meetings — great research discussion and lots of laughs. He was a tremendous mentor to undergraduates and the other new members of our research group.
Congrats Dr. Tueller! You will be missed. Keep on rocking!