As part of an invited session “CAD for Hardware Security” at the IEEE VLSI Test Symposium (VTS), I teamed up with some giants in the hardware security space (Intel, University of Florida, and Tortuga Logic) to discuss the need for security automation tools to enable hardware security verification.
My portion of the presentation focused on the need for hardware security coverage metrics. We developed CWE-IFT that use information flow tracking (IFT) property templates based on common weakness enumerations (CWEs). This describes the current process of security verification followed at Tortuga and within our research group at UCSD.
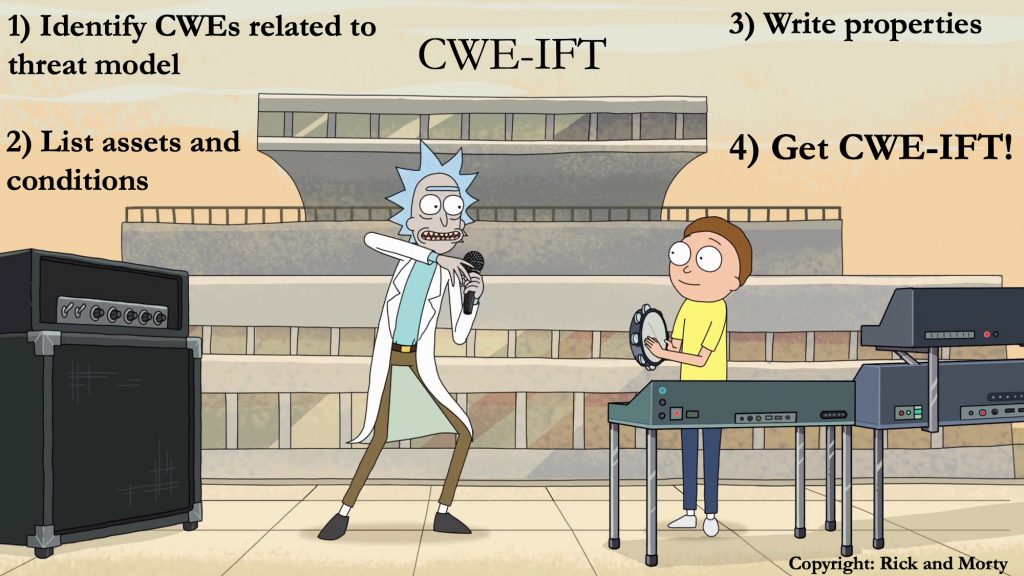
And yes, CWE-IFT is pronounced “Schwifty” after the hilarious (but extremely childish and vulgar — viewer beware!) “Rick and Morty” song. This helps fulfill my childhood goals to incorporate cartoons into my job. See Mom, watching cartoons all day is a productive use of time! 🙂
To understand how to Get CWE-IFT, check out the slides and paper. I promise that they are a lot less childish and vulgar.
Paper: Sohrab Aftabjahani, Ryan Kastner, Mark Tehranipoor, Farimah Farahmandi, Jason Oberg, Anders Nordstrom, Nicole Fern, and Alric Althoff, “CAD for Hardware Security – Automation is Key to Adoption of Solutions”, IEEE VLSI Test Symposium 2021.
Slides: Ryan Kastner, Jason Oberg, Nicole Fern, and Alric Althoff, “Hardware Security Coverage“, IEEE VLSI Test Symposium 2021.